Project Overview
In response to the requirements of a client managing large-scale hydrographical survey projects, JAK Services designed and developed a secure, project-isolated web portal dedicated to the management, visualization, and distribution of survey data and deliverables.
Key Features and Workflows
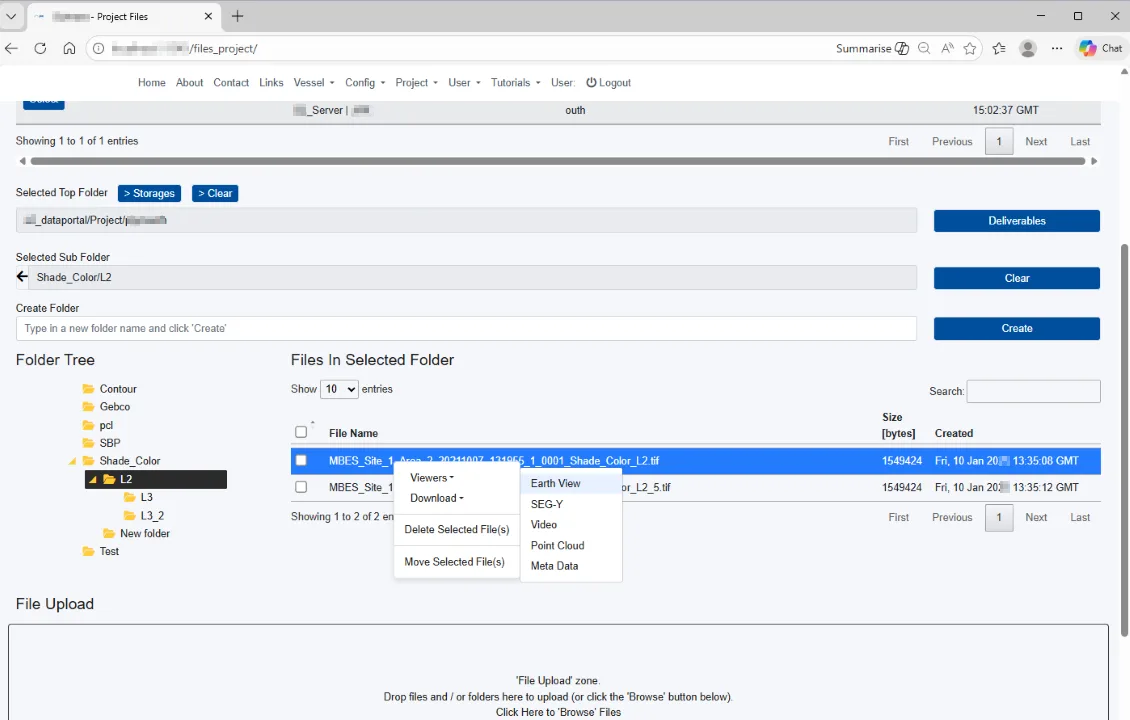
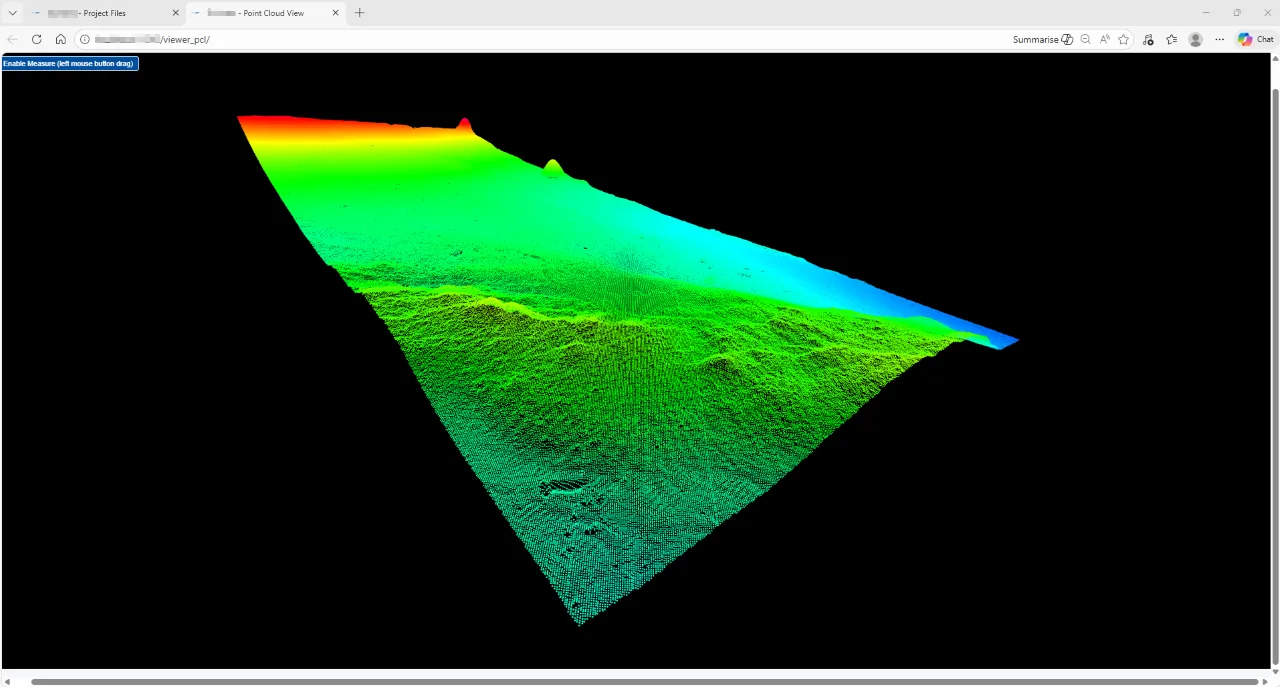
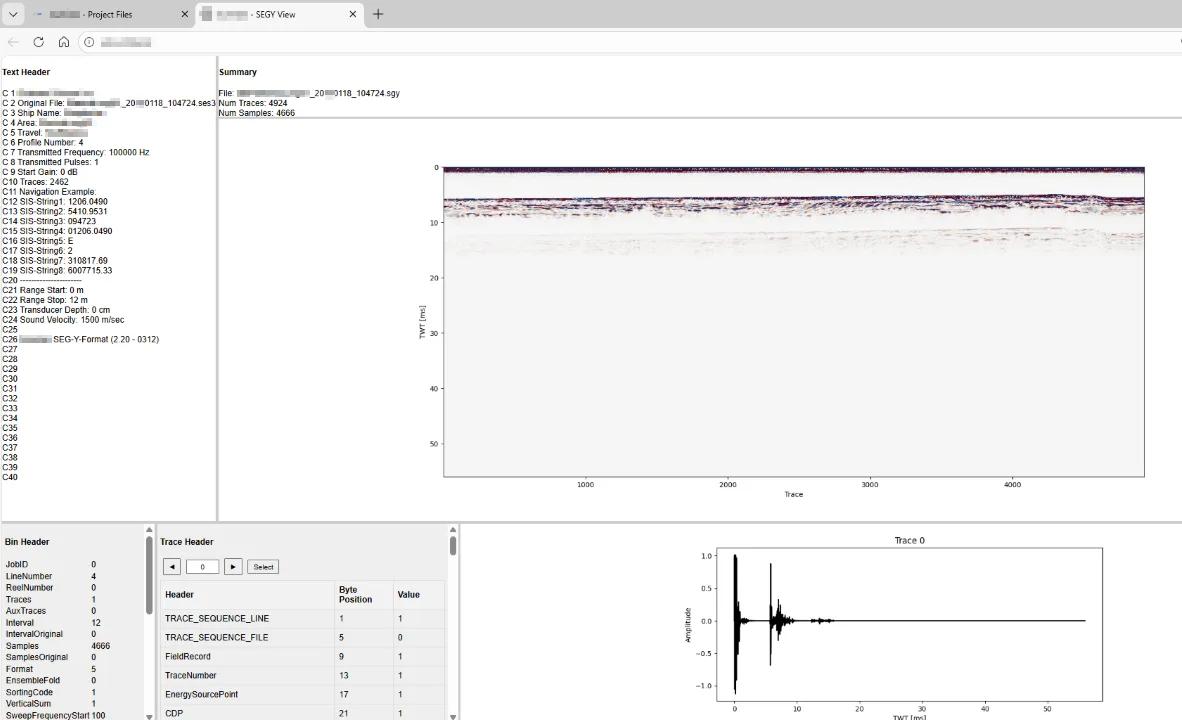
The portal provides file browsing alongside a wide range of integrated viewers:
- Web Map Services (WMS)
- Point-Cloud Viewer
- Sub-Bottom Profiler Viewers
- Video Playback
- and additional format-specific tools
Per-project access control ensures that upload and download workflows are governed by individual user credentials and configurable size limits.
Data Management and Storage
The system connects seamlessly to multiple storage backends, including cloud-based storage solutions, enabling efficient handling of large survey datasets streamed from survey vessels and onshore processing environments.
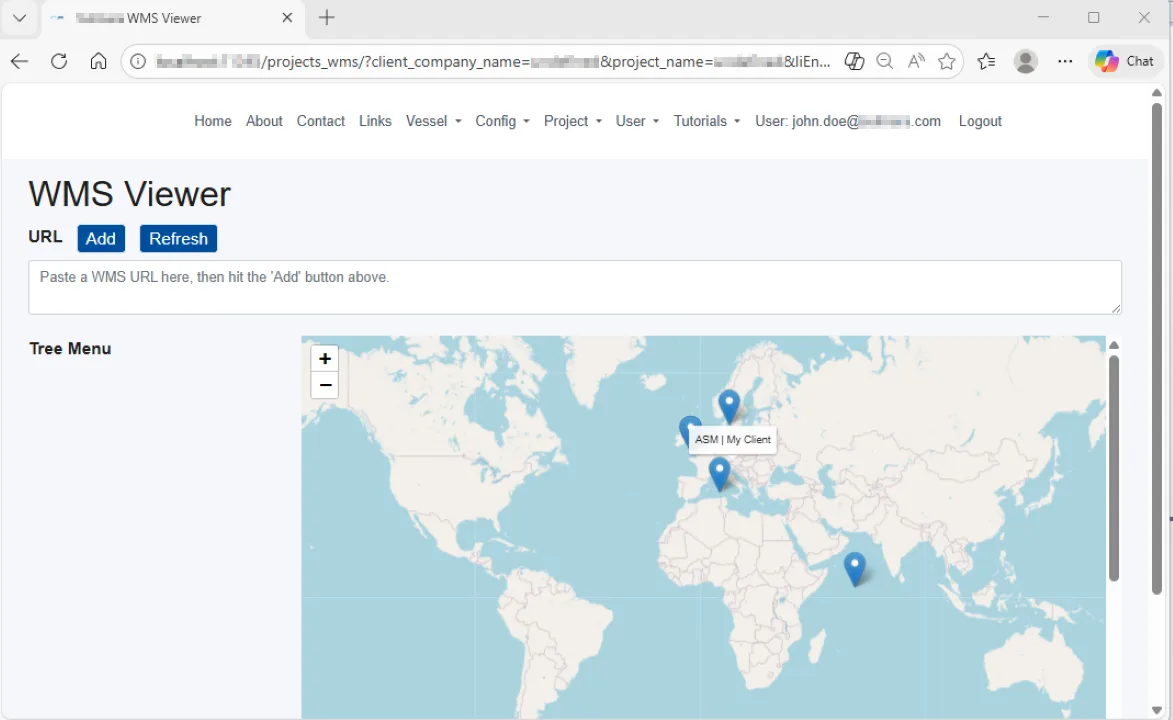
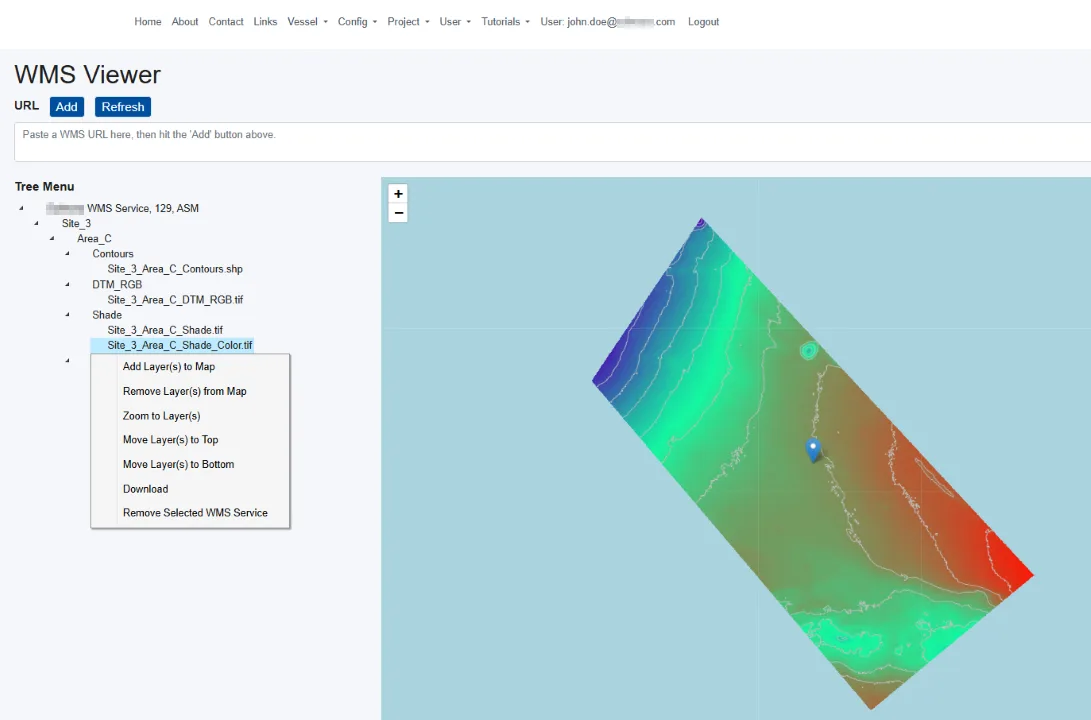
WMS Processing and GIS Integration
The WMS component is supported by background workers that automatically convert GIS data into WMS layers as low-volume datasets are streamed to the portal.
A tree-view layer manager allows users to add, organize, and reorder layers while providing a consolidated overview of all projects accessible to the user.
Published WMS layers can also be consumed by desktop GIS applications and other WMS-enabled portals.
Security
The portal was designed with a “least privilege” approach, combining project isolation with role-based permissions to ensure each user only sees and accesses the datasets relevant to their role, project, and client organization.
- Authentication: email/password login with hashed passwords, plus password policy checks (length/complexity) and password expiry / first-login change flows.
- 2FA (email OTP): a session-bound one-time code sent by email and verified before granting access.
- Brute-force mitigation: login attempt counters with lockout and API-side throttling when abused.
- Authorization (RBAC + project scoping): roles and per-user / per-project assignments, including granular permissions (read/write/delete/download).
- SQL injection mitigation: ORM-based data access and parameterized queries.
- Web & transport security: HTTPS (TLS), CSRF protection, CORS configuration, and browser hardening via security headers (CSP / HSTS where enabled).
- Audit-friendly logging: central application and API error logging to a dedicated log store for traceability and incident analysis.